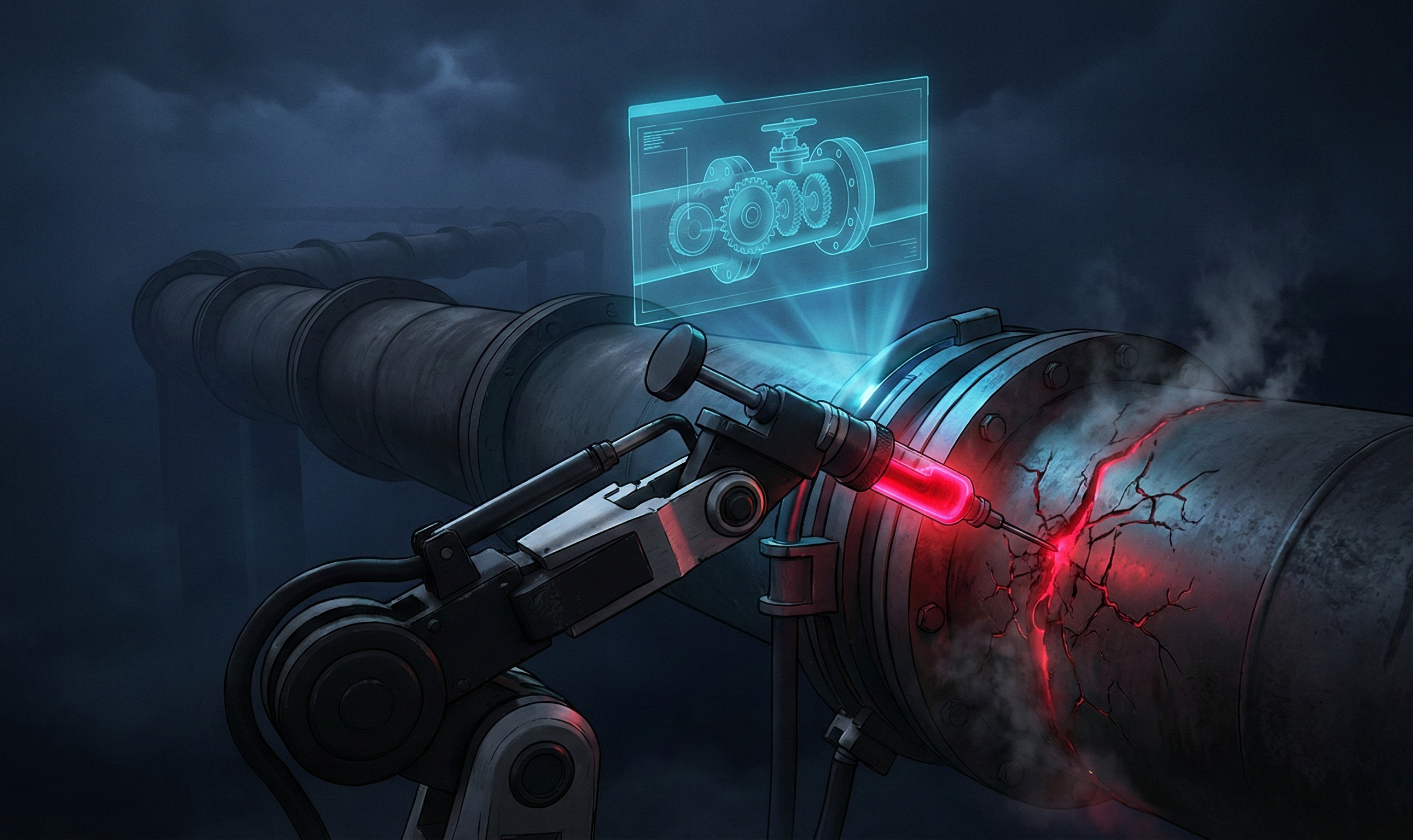
MegaGame10418: A Throwaway Account Linked to the Hackerbot-Claw Attack
Between February 27–28, 2026, the GitHub user 'hackerbot-claw' launched an automated Pwn Request campaign targeting eight high-profile repositories using the AI agent 'openclaw.' Our Package Threat Hunter caught the attack in progress. Further investigation revealed 'MegaGame10418'—a throwaway account that predated the campaign by a month—used to test the same injection techniques against a vulnerable NewRelic test repository.